En hébergement mutualisé
Anti-spam measures in shared hosting
Reminder! For the security of your sites, you must:
- Enable the https protocol for your domain,
- Apply the non-cumulative patch to each release of a new version, update your plugins,
- Set up administrative protection for administrators and collaborators who have access to the administration of the site,
- Regularly update your machine's software (pc, tablet, smartphone),
- Rename sensitive files to admin/config services,
- Avoid the use of external scripts in GuppY,
- Enable all protection modes offered by your host,
- Use secure passwords, at least 8 characters with lower case, upper case, numbers and special characters,
- Do not delete the.htaccess at the root of GuppY, nor the.htaccess in the directories,
- Use an up-to-date antivirus software, browser and search engine that respect your privacy.
If this has not yet been done, we invite you to do so as a matter of urgency.
In the GuppY 5.02.06 package here is the content of the .htaccess of the GuppY root :
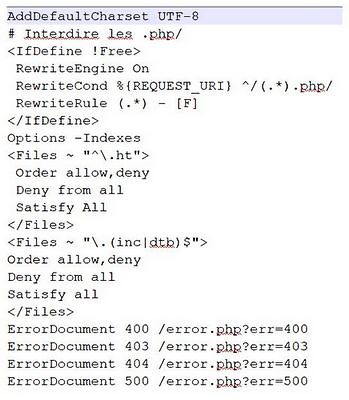
After the line: ErrorDocument 500 /error.php?err=500, you must include two empty lines.
If you have additions to make in the.htaccess file, do them before the ErrorDocument 400 line /error.php?err=400
We will add at the beginning the blocking of spammers' IPs:
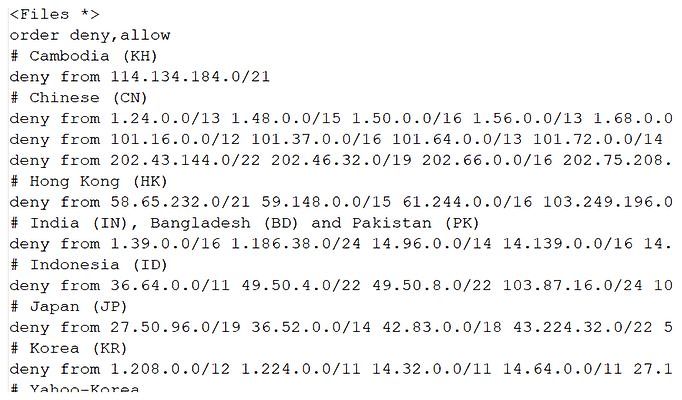
This list is adapted from this link: https://www.wizcrafts.net/chinese-blocklist.html
The .htaccess can vary according to the hosts, so the first thing to do is to read your host's documentation and check that it complies with your host's recommendations.
Their behavior being different according to the sites, and the very frequent IP modifications this list must be updated and evolve according to the observations you can make in the logs of your site, those of GuppY in admin/logs, or those provided by your host.
If you haven't already done so, it's time to go to admin/logs, configure the GuppY logs and set the maximum number of logs to keep.
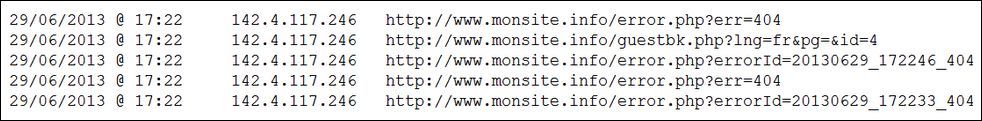
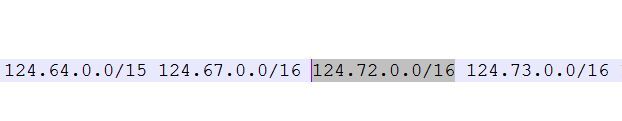
or a similar IP address:
29/06/2013 @ 08:54 124.72.69.69.72 72.69.72.72.124.board.xm.fj.dynamic.163data.com.cn
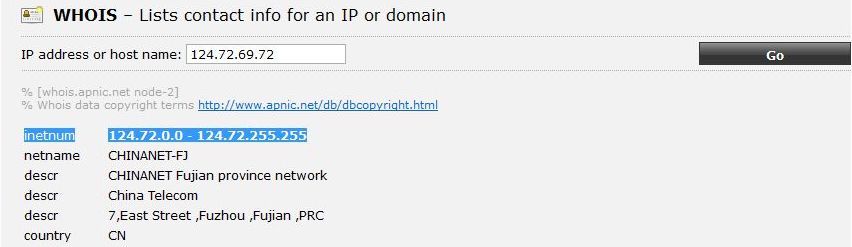
To know the range of this IP, we go to this site: https://ping.eu/ns-whois/ and we see on the first line :
inetnum 124.72.0.0.0 - 124.72.255.255.255
Pour la bloquer, sur le même site, nous allons cliquer sur le lien « Network mask calculator » en bas de page,
Voici le résultat :
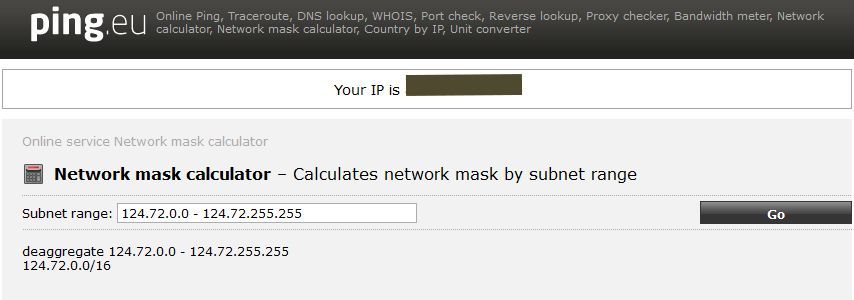
For the blacklisting we will have to add in the list 124.72.0.0.0/16 .
This is done with the example below:
The number of IPs of Chinese or Asian spammers should almost disappear from your logs. Be careful, it is true today, it does not mean that this will be the case in the coming days or weeks.
The objective is not to blacklist all the IPs on the planet, so you should check the ip you suspect before blocking it.
In the zip archive on freeguppy.org, you will find a file htaccess.txt, you copy/paste the content from Notepad++, before the first line AddDefaultCharset UTF-8
If it is possible on your hosting, you can chmoder it in 404, check beforehand to avoid a complete crash.
Tutorial realized by Papinou for the GuppY Team - March 2013 - Update Septembre 2018 - License Libre CeCILL